Deploy a GDPR Governed Data Access framework with Qlik to assist your compliance process for GDPR.
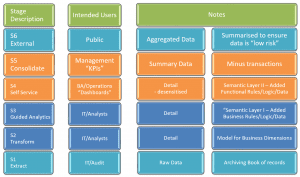
Both structured and unstructured data is required to comply for GDPR. Differentia Consulting has redefined its #SmarterBI methodology to assist in helping clients comply with structured data compliance by offering a Governed Data Access Framework that consists of 6 stages.
Preparing for GDPR
The briefing 28.02.17 (Further Reading-below) covers The European General Data Protection Regulation (GDPR) on cyber security, and highlight the key things that organisations need to know about its implementation, including its impact on how businesses can use data, key tips on how to start preparing for the Regulation, and how to articulate a clear privacy policy.
The UK’s economy is underpinned by the ability to analyse and move data. In fact, soaring data flows now generate more economic value than the global goods trade, raising world GDP by approximately 10 per cent over the last decade. As the leading digital economy in Europe, the UK has the most to gain, and conversely the most to lose, from the European data protection landscape.
The ways in which companies use this data and move it across borders is governed by strict data protection regulations. Critically on 25 May 2018 the GDPR will apply to UK law despite the Government’s pledge to begin the Brexit process in March 2017. This will provide a wide-ranging new legal framework for data protection regulation in the EU.
Despite the threat of financial penalties for non-compliance with the Regulation, 50% of global companies have admitted that they will struggle to meet its rules unless they make significant changes to how they operate.
ISO 27001 and GDPR: How can ISO 27001 help?
The General Data Protection Regulation (GDPR), agreed in December 2015 and refined in early 2016, sets out new laws to govern the security of personal data for organisations in EU member states (and the UK, despite Brexit). The directive has been established to standardize one set of rules across Europe which will ensure stricter control of organisations processing personal data, issuing significant fines for non-compliance. But how do ISO 27001 and GDPR work together? Can compliance with ISO 27001 ensure compliance with GDPR requirements? And which controls in ISO 27001 compliment GDPR?
We must firstly understand what constitutes personal data in relation to GDPR. Well, like in the Data Protection Act (DPA) personal data is defined as any information relating to an individual who can be identified, directly or indirectly, by that data or set of data. This means that any names, identification numbers or locations that can be used to identify an individual constitutes personal data. In isolation, this may not reference an individual i.e. a username, but when used with a personal name, address and postcode this becomes personal data as it is attributed to an individual. One point that is often overlooked is that online data, including IP addresses, cookies and other data extracted from web browsers can be regarded as personal data if a person can be identified as a result of that data.
How does ISO 27001:2013 currently support protection of personal data?
Within Annex A controls, A.18.1.4 Privacy and Protection of Personally Identifiable Information (PII) requires organisations to protect PII in line with relevant legislation and regulation. For organisations trading in the UK, this is currently the DPA but will move to GDPR by 2018. ISO 27001 recommends implementing a data protection policy specifying requirements for data protection supported by specific procedures regarding aspects of data protection e.g. retention and destruction. ISO 27001 also recommends implementing appropriate organisational and technical controls to support compliance with these requirements. As we can see, protection of PII and compliance with legislation is already a key control requirement in ISO 27001 – so this supports compliance with GDPR.
What controls can be implemented to support GDPR compliance?
Other ISO 27001 Annex A controls can also be used to support GDPR compliance. A.10.1 Cryptographic Controls specifies encryption requirements for the organisation, and these technologies can be used to protect personal information when at rest or in transit on the network. The use of encryption and/or pseudonymisation can maintain the confidentiality of personal information, whether on the network, transiting or on mobile devices.
GDPR identifies data controllers and data processors, obligating controllers to only engage processors that provide sufficient assurance that controls are in place to manage personal data. This is a similar approach used in ISO 27001 to manage suppliers and third parties, as defined in A.15 Supplier Relationships. By assessing data processors against a code of connection or an approved certification, data controllers can demonstrate compliance. These requirements should be documented and in agreements between controllers and processors.
A further control is business continuity management (A.17), where controls can be used to ensure the on-going availability of personal data to those who require it, a key tenant of the DPA, ISO 27001 and GDPR.
In addition to the above and other controls with Annex A, the formation of an information security management system enables organisations processing personal data to demonstrate that risks to personal data are being continuously reviewed, update and improved. An established ISMS is the perfect framework to manage risks to all assets, inclusive of personal data, and can provide assurance that the organisation takes ISO 27001 and GDPR compliance seriously. source: http://iso27001guide.com/annex-a/compliance/compliance-with-legal-and-contractual-requirements/iso-27001-and-gdpr/
GDPR Additional Information
ISO 27001 and GDPR GDPR References and Further Reading Articles Qlik Governed Data Framework







